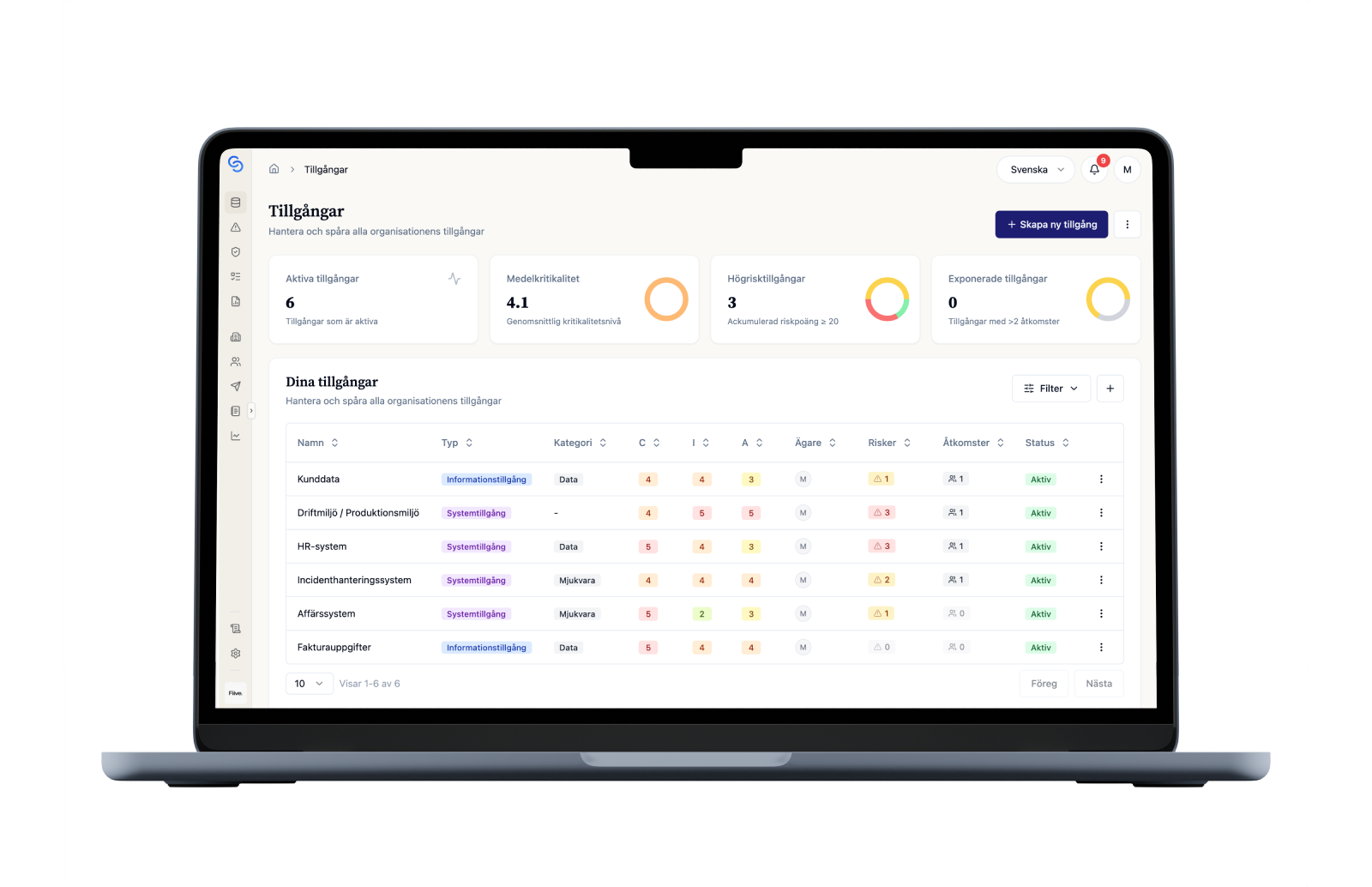
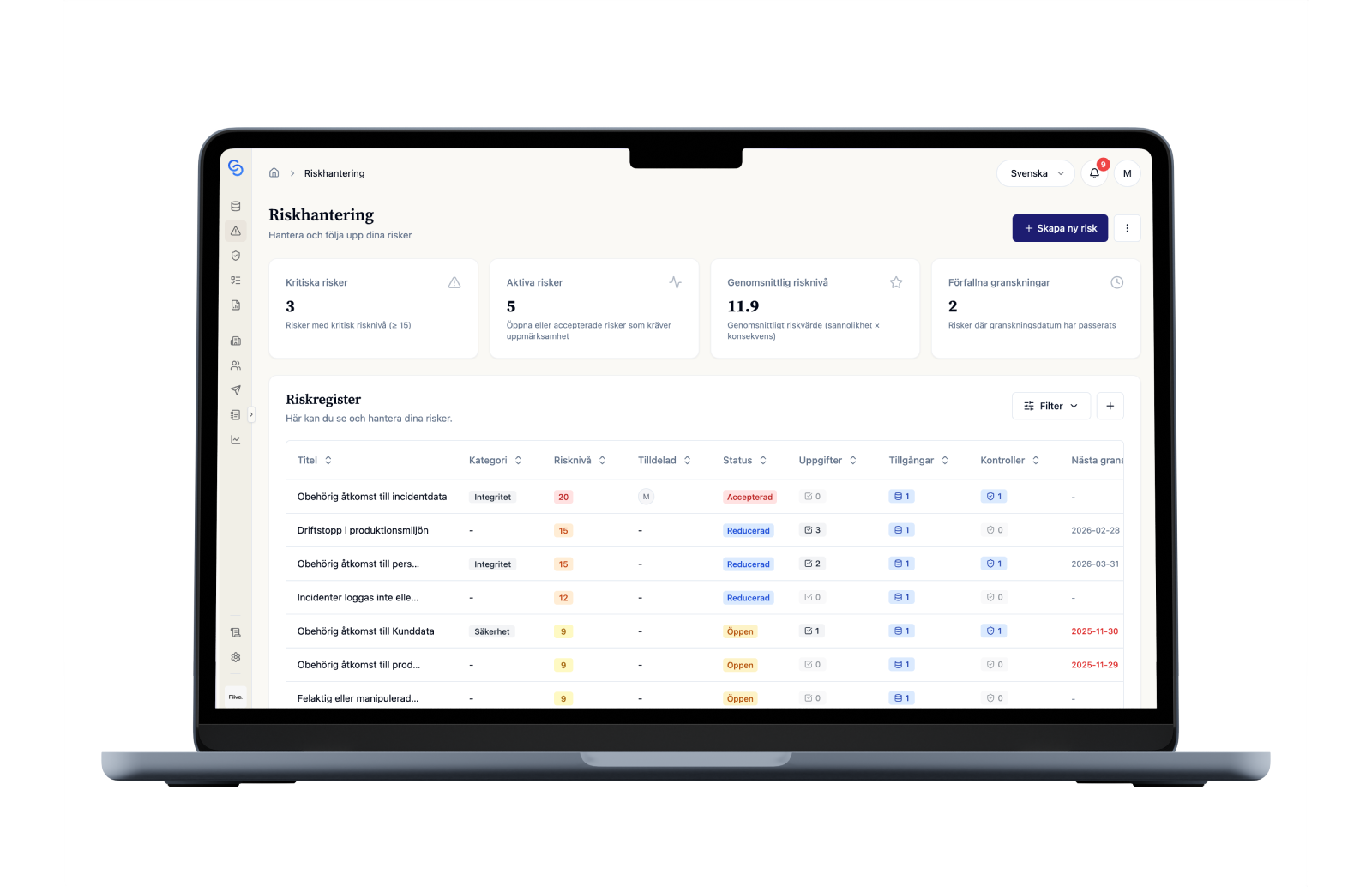
Create one shared register for critical assets
Document systems, information assets and other critical objects in a register where you can see owner, classification, business value and relationships. That makes it much clearer what is worth protecting and how priorities should be set.
Book demo